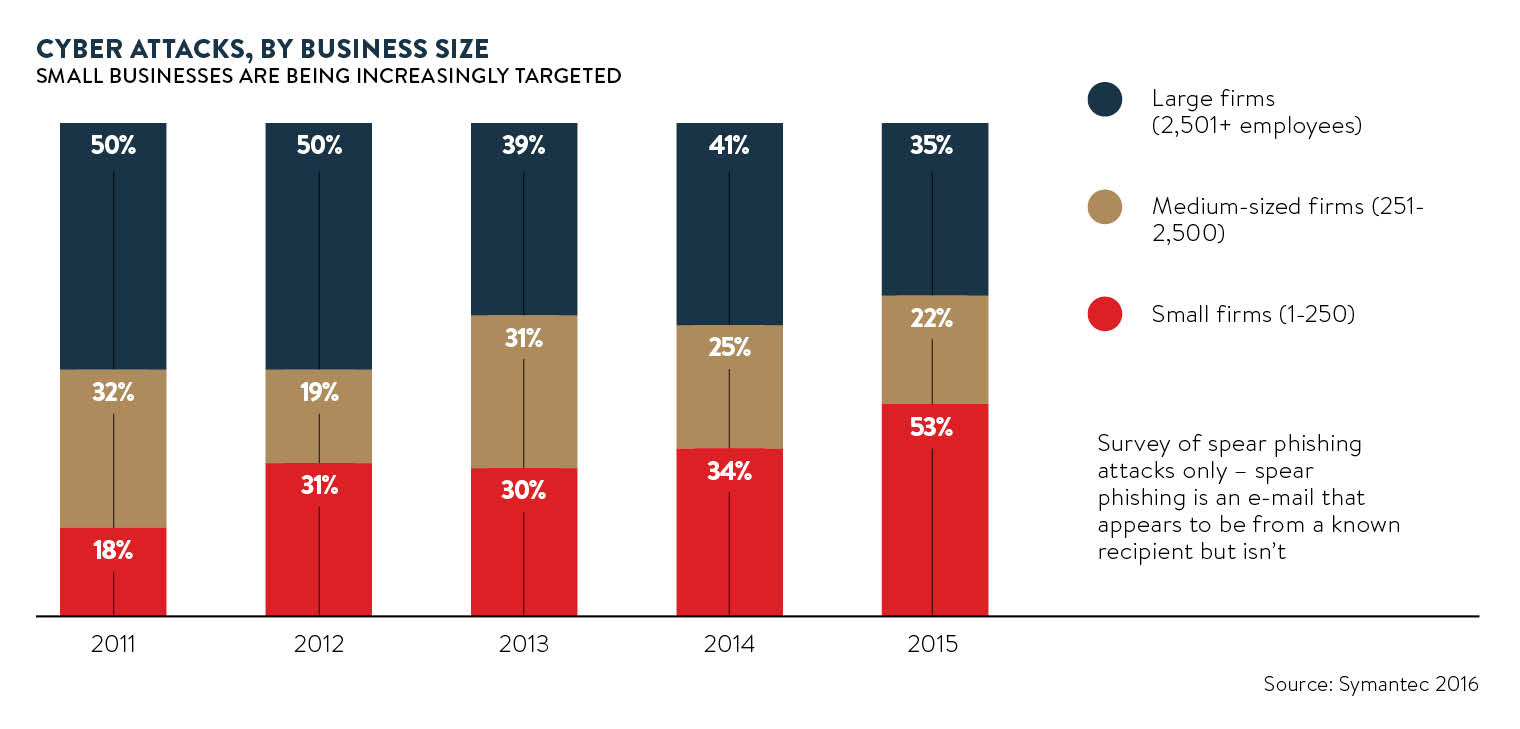
Cyber attacks against big businesses are nothing new, with high-profile companies falling foul of sophisticated online criminals at an alarming rate. A cyber attack on a smaller enterprise is unlikely to get anywhere near the level of publicity garnered by the hacking of a multinational corporation, but this doesn’t mean there aren’t many successful attacks against small firms on a daily basis.
Data held by small and medium-sized enterprises (SMEs) is becoming increasingly valuable to cyber criminals. According to recent research released by Barclaycard, 48 per cent of SMEs fell victim to at least one cyber attack last year and 10 per cent were targeted multiple times.
Cyber criminals are targeting SMEs in a growing number of ways, with ransomware attacks proving to be one of the most popular methods used to extract money. Ransomware is a type of malware that encrypts all files on a computer and demands money, usually untraceable bitcoins, for them to be unlocked. Not only do 36 per cent of ransomware victims report loss of business income due to the attack, but this type of cyber threat is expected to increase 300 per cent from 2015 to 2016, according to insurance research provider Advisen.
One thing that links SMEs to large organisations is they are equally at risk to cyber attack – no one is immune
“The impact of a successful attack on hard-won reputation, supply chains and operations can be catastrophic for an SME,” says Nick Wilding, general manager of cyber resilience at IT best practice organisation AXELOS.
In recent years, the average SME has gone from using predominately simple siloed solutions to embracing more interconnected systems. From bring your own device (BYOD), off-site working to the cloud, small businesses have never been more connected to their clients and therefore more open to threats.
So why are so many SMEs still unprepared for a cyber attack?
Mr Wilding believes that SMEs usually have markedly different priorities than larger corporations, such as maintaining a strong cash flow and ensuring the right mix of skills and expertise is retained within their small teams.
“These pressures all mean that cyber risk is often not seen as a critical business risk by SMEs. But one thing that links SMEs to large organisations is they are equally at risk to cyber attack – no one is immune,” says Mr Wilding.
Patrick McLoughlin, director at marketing firm Accounting for Growth, agrees. “We take cyber risks very seriously, but as a small business we have so many different priorities to contend with, which means cyber issues aren’t always at the top of the list. The problem is businesses don’t take it that seriously until it’s too late or you hear that it’s affected someone you know,” he says.
Cyber criminals are also taking advantage of the central role SMEs play in the wider economy and exploiting their online weaknesses to gain access to bigger targets. “SMEs are a growing target for hackers as they can be the pawns that lead to the ‘crown jewels’ within a much larger organisation. Many SMEs will be connected electronically to the IT systems of larger business partners, the companies that the cyber criminals really want to get at,” says Kevin Bocek, chief security strategist at cyber security firm Venafi.
Risk awareness
 The UK government has launched a range of schemes aimed at helping SMEs improve their cyber-security capabilities, with a recent scheme offering up to £5,000 to spend on cyber training and advice. Unfortunately, there is still a long way to go until SMEs are appropriately resilient to cyber threats. According to Barclaycard, only 15 per cent of small businesses are very confident they have adequate measures in place to defend against a cyber attack, indicating that government messages are falling on deaf ears or not being adequately amplified.
The UK government has launched a range of schemes aimed at helping SMEs improve their cyber-security capabilities, with a recent scheme offering up to £5,000 to spend on cyber training and advice. Unfortunately, there is still a long way to go until SMEs are appropriately resilient to cyber threats. According to Barclaycard, only 15 per cent of small businesses are very confident they have adequate measures in place to defend against a cyber attack, indicating that government messages are falling on deaf ears or not being adequately amplified.
“I am not aware of any government push to advise or assist small businesses about cyber crime and how to protect against it,” says Adam Tierney, managing partner at law firm Tierney & Co. “Ultimately, I think we need to be responsible for our own destiny in this respect and rely on ourselves. Paid help is out there if we can’t do it ourselves, but perhaps if the government drew greater attention to the importance of cyber security and a means of getting impartial advice, this would help.”
External cyber attacks are often viewed as the most pressing threats that SMEs need to protect themselves against, but an increasing number of fraudulent cyber activities are originating from within an organisation itself. Ryan Rubin, managing director at consulting firm Protiviti, believes that disgruntled staff who seek to steal company information and secrets can pose a serious danger to vital company data.
“Such events could be devastating for SMEs, for example, if their business plans or intellectual property is stolen. As there are usually key-person dependencies within SMEs, this presents a real risk to many,” says Mr Rubin.
The rise of cyber crime
The movement towards increasing interconnectivity in businesses of all sizes can only be expected to provide new avenues for unscrupulous employees to take advantage of cyber-security weaknesses. A large number of cyber breaches are a direct result of human error, with Protiviti recently investigating a fraud committed by a finance clerk in one of their client’s shared service centres. The employee had accidentally been given wider access to the client’s supplier payment systems than they should have and close to £300,000 worth of unauthorised transfers were made.
Incidents like this are possible if the proper protocols for monitoring and managing user identities are not followed. Cyber criminals are now using social engineering techniques to exploit this weak link in security by tricking employees into handing over sensitive information. One method hackers use is pretending to be a supplier or client and e-mailing over what appears to be an invoice, but the attachment contains malware. These types of attacks are surprisingly effective as all it takes is a single employee to click on a link and the entire system is compromised.
“If criminals can trick the chief financial officer or finance director to transfer £20,000, with an e-mail that looks like it came from the founder, managing director or chief executive, then it doesn’t matter how small a company is,” says Richard Walters, senior vice president of security products at cloud business application provider Intermedia.
The ease in which cyber criminals can exploit human vulnerabilities should of course be a cause of concern for SMEs. Employees of small businesses should be aware of the methods used by cyber thieves. IBM’s Cyber Security Intelligence Index found that 95 per cent of all security breaches involve some level of human error, highlighting the importance of educating staff in the best cyber-security practices.
Action to take
“For SMEs, it’s as much about education as technological solutions, as there isn’t particularly a cost-of-tech barrier,” says Paul Billington, managing director of digital marketing agency Prodo Digital.
Just because SMEs spend far less money and time implementing digital security solutions than major corporations, this doesn’t mean that hackers are targeting smaller firms individually. “Any attacks against an SME will likely be by opportunists. There’s no point in going out to get your network pen-tested, installing the latest firewalls and insisting all your staff are security-screened by MI5 if you don’t work with any data that is sensitive,” adds Ed Yau, Prodo Digital’s head of development.
It can be difficult for SMEs to find the right balance between protecting themselves from malicious cyber attacks and creating unnecessary restrictions on employee device usage. Jon Moger, senior director at Aruba, a Hewlett Packard Enterprise company, says that while it’s crucial to nurture creativity in an SME’s workforce, a contingency plan should be put in place for cyber attacks.
“Inevitably, this puts a lot of pressure on IT to take an adaptive, trusting approach to device connectivity and data security,” says Mr Moger. “There must be a mechanism for employees to provide feedback to IT, and a service level agreement should be in place for how to respond to employee input and requests.” The success of IT policies can often be improved by simply listening to employee feedback, he adds.
With the threat from cyber criminals not expected to disappear anytime soon, SMEs need to adapt effectively to the preferred behaviour of their workforce. “Embracing the need for openness, innovation, collaboration and some degree of risk is good, but only when an organisation can understand and plan for the security risks these behaviours bring with them,” Mr Moger concludes.
Risk awareness