Capgemini’s The Modern Connected CISO report revealed 60 per cent of organisations have their CISO at key board meetings, but only half of business executives think the role has a high level of influence on management decisions. This could be because less than a quarter of executives thought information security was a proactive enabler of digital transformation. But just as easily it could be that C-suite and cybersecurity experts don’t talk the same language.
Without a more cohesive working relationship between the CISO and chief executive, chief financial officer and chief operating officer, the organisation will never move at the speed of trust that is required by current agile business demands.
“Business leaders often choose to take risks while cybersecurity teams are trained to mitigate risk, which means priorities are at odds,” says Greg Day, chief security officer, Europe, Middle East and Africa (EMEA), at Palo Alto Networks. Fixing this disconnect between the CISO and the rest of the C-suite is therefore key to building cyber-resilience through an informed risk management strategy.
CISO still struggling to be heard by the rest of the board
So where are the most common disconnects to be found? That many CISOs find being heard at the top table still a work in progress, rather than a done deal, is part of the problem. “CISOs, though growing in prominence, still struggle to wield influence at board level,” says Keiron Shepherd, senior security systems engineer at F5 Networks. F5 research from last year showed 19 per cent of CISOs reported all data breaches to their board of directors, and 46 per cent admitted chief executive and board-level communications only happen in the event of material data breaches and cyberattacks. “This is a serious strategic disconnect,” says Mr Shepherd.
Or how about the responsibility for day-to-day security which, for many businesses, doesn’t fall squarely on any one person’s shoulders?
“The narrow gap between the roles of chief information officer, chief executive and CISO shows that no one executive function is stepping up to the plate,” says Azeem Aleem, vice president of consulting at NTT Security. “Given escalating threat levels and increasingly acute regulatory challenges, there’s an urgent need for clear reporting lines and a foreground role for the CISO.”
Ian Bancroft, general manager, EMEA, at Secureworks, agrees that all too often it takes a breach before the CISO is asked to present to the chief executive and board. “Developing the right communications flow is the key to ensuring that business leaders appreciate the risks and mitigation strategies,” he says.
The CISO needs to get better at aligning with business needs
 The commonplace situation of the CISO presenting an annual risk report to the board, with everything else across the year being made by their boss, usually the chief information officer or finance chief, can mean security status reporting often takes on the bias of whoever that happens to be.
The commonplace situation of the CISO presenting an annual risk report to the board, with everything else across the year being made by their boss, usually the chief information officer or finance chief, can mean security status reporting often takes on the bias of whoever that happens to be.
The CISO undoubtedly needs to be able to communicate effectively with the senior leadership team. They need to be able to grasp complex issues relating to risk and get these across in a way that secures the buy-in needed. “Yet many CISOs will have had no prior leadership experience,” argues Chris Underwood, managing director at Adastrum Consulting. “As such, they will have limited knowledge of how to operate at executive level and speak ‘executive’ language.” Which brings us to the biggest problem for cybersecurity: lack of alignment with the business.”
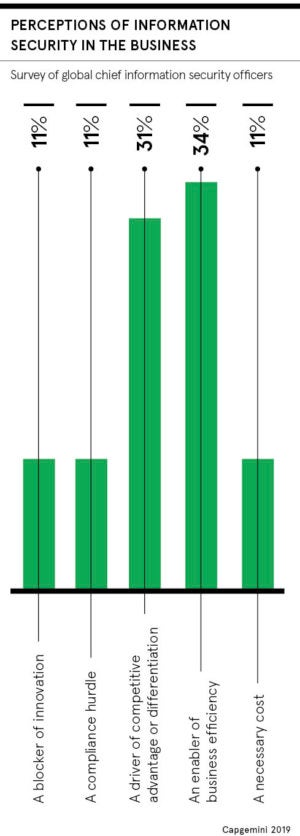
CISOs have traditionally been seen as running business prevention units,” says Institute of Information Security Professionals chief executive Amanda Finch, who explains they are often thought of as “prophets of doom, scaremongers and a drain on the business”. Clearly, CISOs must demonstrate they are on the same side. “They need to speak to chief executives and chief financial officers in language they understand to provide a common understanding of the real risks that an organisation can face,” Ms Finch concludes.
The CISO must be able to put cyber-risk in a business context
Being able to articulate risk in a business context, alongside realistic and cost-aware solutions, is central to this relationship-building exercise between the CISO and the board. “This is easier said than done though,” warns Sam Curry, chief security officer at Cybereason. “It requires soft skills, patience, gravitas, and sincere enthusiasm and participation in the business.”
Which, according to Mr Curry, involves the use of just six key terms: revenue, cost, risk (this is the big one), customer satisfaction, employee efficiency and company strategy.
Simon Roe, product manager at Outpost24, says: “Each C-suite member needs to have an understanding of the business risks associated with a major breach.” Whether that’s costs associated with running a cybersecurity programme, reputational impact or financial penalties associated with an unreported breach, it’s all part of a security culture.
Eoin Keary, chief executive of edgescan, sums it up: “There should be a conscious effort with one side committing to learning about cybersecurity and the other to make cybersecurity understandable to a layperson who has a different area of expertise.”
CISO still struggling to be heard by the rest of the board
The CISO needs to get better at aligning with business needs