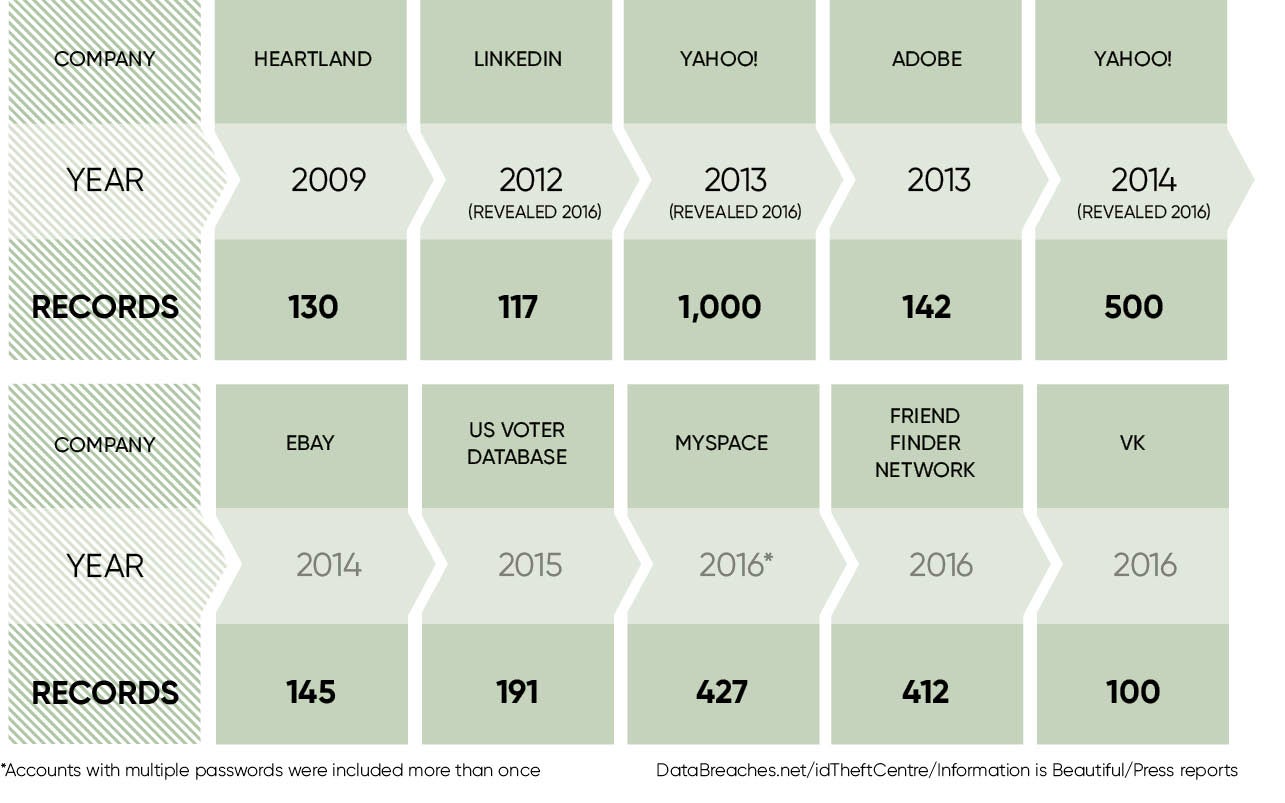
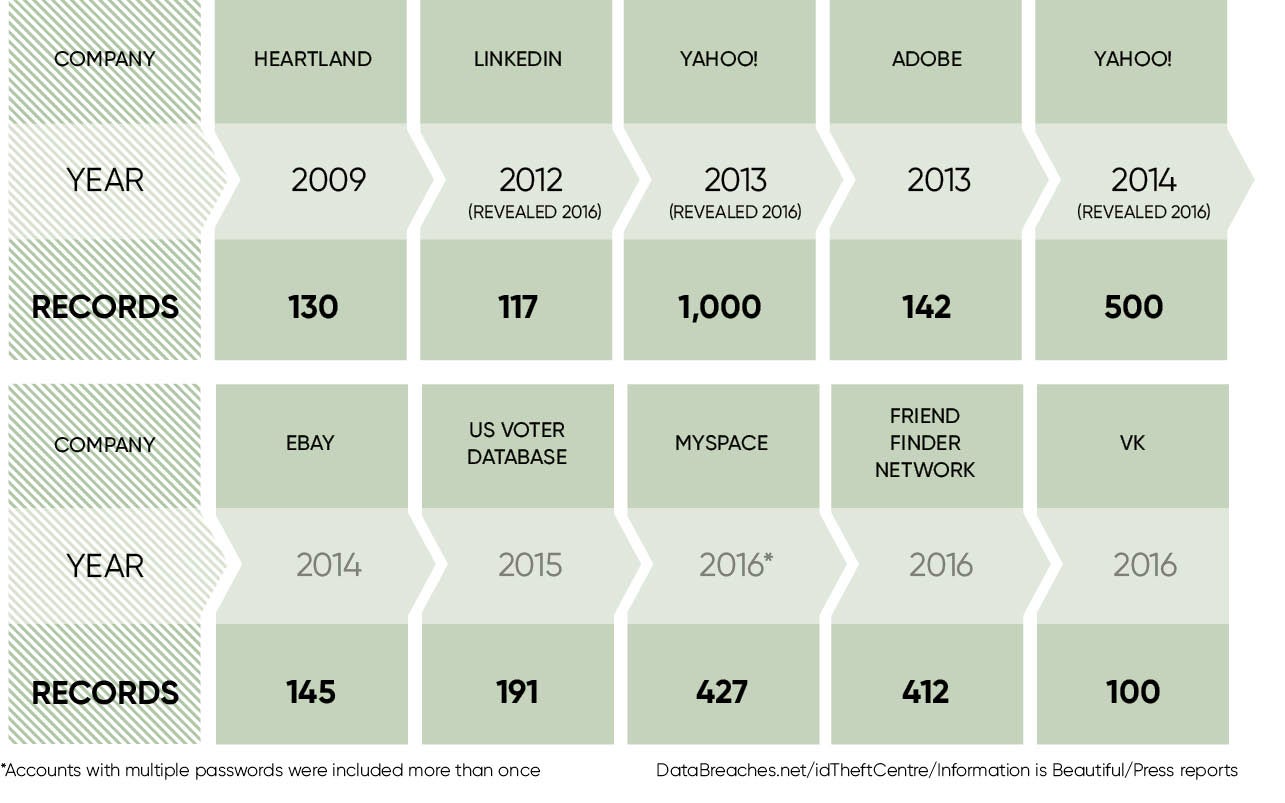
Yahoo! was once best known for being the search engine that lost out to Google in the nineties, but went on to become an internet giant acquiring blogging platform Tumblr in 2013 for $1 billion in cash. Today it’s better known for falling victim to the biggest cyber-security breach in history, also occurring in 2013 and involving a billion user accounts.
In addition, it fell victim to attackers in 2014 with a breach that impacted more than 500 million user accounts, the second largest in internet history. It hardly seems fair to mention the most recent disclosure from Yahoo! that revealed hackers accessed a further 32 million accounts using a forged cookie attack, stretching back two years.
This followed a statement in December 2016 confirming data associated with more than one billion accounts, dating back to August 2013, had been stolen. To compound how bad things have been for the company, just three months earlier it had disclosed an attack involving 500 million compromised accounts from 2014.
That Yahoo! is facing several lawsuits in the United States and abroad, as well as investigation by members of the US Congress, could explain why requests for comments go unanswered by its press office.
In fairness if, as Yahoo! chief information security officer (CISO) Bob Lord claims, state-sponsored actors were behind both the 32 and 500-million account breaches, it’s hard to be too critical. Four people have now been indicted by a US grand jury over the latter attack, two of them officers in the Russian Federal Security Service (FSB) so it looks like Mr Lord was right. And if a state-sponsored attacker wants your data, they are likely to get your data.
I’m hoping Yahoo! is the catalyst that will exact some meaningful change
But that doesn’t mean you should make it easy for them. Among the account data stolen were hashed passwords, yet Yahoo! could have made things harder for the attackers by not using an outdated algorithm called MD5. Hashing is a one-way function, a mathematical operation that is easy to perform but hard to reverse, used to enable verification of passwords without having to store the password itself.
While most stolen passwords used the well-respected bcrypt algorithm, many used the easy-to-crack MD5 algorithm, despite the weakness of this being common security industry knowledge for at least a decade. It was a mistake for Yahoo! not to replace this fully long before the attacks took place, as was being aware of the 2014 attack at the time, but failing to comprehend the seriousness or adequately investigate it.
Although Yahoo! has said that it has “revised” procedures for responding to cyber-security incidents, it is not clear currently what else has been done to beef up the security posture. We know it forced password resets for some, but not all, users. We know it required new security question responses for all one billion accounts caught up in the 2013 breach. We know all the cookies involved in the 32-million account compromise were revoked to prevent that access route. Beyond that we know very little.
So what does the cyber-security industry make of it all?
Simon Edwards, European cyber-security architect at Trend Micro, says: “The first lesson to learn is that companies must invest more in technology and staff training, which allows them to find the breach when it happens, ideally stop it before it causes damage and not months later.”
Nigel Hawthorn, chief European spokesman at Skyhigh Networks, reminds us that data loss has a very long tail. “The company’s value has dropped by around $350 million,” he says, “and that’s ignoring the regulatory fines, and the fact that the CEO will step down upon completion of the Verizon takeover.”
But what should the chief information officer (CIO) of tomorrow take away from the mistakes of yesterday as shown so clearly in the Yahoo! breaches? Chris Pogue, cyber-security instructor to the US Secret Service Electronic Crimes Task Force as well as the CISO at Nuix, says: “Listen to your security teams. They were hired for a reason. In the case of Yahoo!, it appears senior executives did not properly comprehend or investigate what the information security team knew and they failed to act sufficiently upon it.”
To stand the best chance of protecting data, CIOs must harness and grow what they know by adopting a consistent framework for sharing and using intelligence. “I’m hoping Yahoo! is the catalyst that will exact some meaningful change,” Mr Pogue says.
The CIO is a critical cog in the security machinery, and must pull in all relevant resources to prepare for and oversee breach response. Oliver Pinson-Roxburgh, Europe, Middle East and Africa director at Alert Logic, says the worse media coverage he has seen is when the CIO isn’t close enough to the response teams so has no clarity regarding a remediation plan for the incident, the impact and the effect on customers. “Lose confidence early,” Mr Pinson-Roxburgh warns, “and you will find it really hard to recover.” It’s a lesson that Yahoo! is learning the hard way.