1. “Biometric data is stored as whole images, so hackers can access my face and fingerprints”
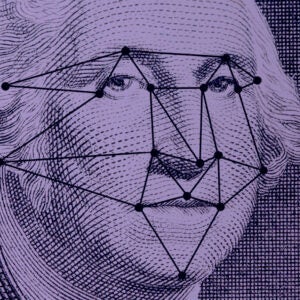
Biometric data is initially extracted from an image, but the image itself is not what’s used in the authentication process. The original sample, whether it’s an image of a face, fingerprint, iris or otherwise, is quickly discarded and replaced by a mathematical file called a biometric template. The template is a digital reference of the unique characteristics found in that initial image.
“The characteristics of a biometric such as a face or fingerprint can be encoded mathematically into a much smaller representation that is easier to store and test against,” explains Kevin Goldsmith, chief technology officer at Onfido. “This mathematical representation is still considered personal data because it is unique to a person, but it doesn’t let a hacker see a photo of a face or fingerprint.”
There are a number of methods used to safeguard these biometric templates, including distributed data storage. This technique stores smaller, encrypted biometric data in a number of locations, like on a server and a smartphone.
“Having biometric data encrypted in this way renders it useless to a hacker,” says James Stickland, chief executive of Veridium. “This can be done without making any organisation the custodian of the data, as biometric templates can be stored in a decentralised location, leveraging this distributed model and effectively minimising the risk of a data breach.”
2. “Biometrics are easy to replicate”
It is possible to duplicate biometric data in the form of a fingerprint or face by using methods such as 3D-printed fingerprints or replica heads, but it’s certainly not easy or commonplace.
In general, biometric technology incorporates a number of features or stages in the authentication process. A fingerprint, for example, is often combined with a contextual signal like fake device detection or expected location.
“Despite what we see in Mission Impossible or similar action movies, biometrics are actually quite difficult to replicate,” says Dr Toby Norman, co-founder and chief executive of Simprints. “The large majority of vendors have implemented liveness detection and other forms of anti-spoofing within their solutions that render it increasingly challenging to fake a biometric.”
Liveness detection algorithms can analyse images to distinguish between a bogus attempt made by someone using a reproduction and an authentic attempt made by a live human being.
3. “Biometric data is unreliable and error rates are high”
Sceptics may question the reliability of biometric technology, but evidence shows it’s far superior to outdated methods such as password authentication.
Password verification accounts for more than 80 per cent of cyber breaches, according to a recent Verizon report. Biometric technology on the other hand boasts much better security performance and high accuracy levels.
Decades of technological advancement mean fingerprinting has accuracy of more than 99 per cent, according to a study by the National Institute of Standards and Technology (NIST). Iris scanning is even more precise. A report by the Government Office for Science found low error figures imply that for every 100,000 iris scans, only two mistakes are made.
“By moving away from measures based on what you know, which can be phished and stolen, and instead pairing these with innovative biometrics, such as the way a user interacts with their device, organisations can strengthen security in a way that is frictionless, reliable and transparent,” says Stickland at Veridium.
However, it is worth noting that although biometrics is largely reliable, it isn’t perfect. Artificial intelligence-based technology such as facial recognition is still hampered by racial biases. A recent NIST study of facial recognition algorithms in the United States found that Asian and African-American people were up to 100 times more likely to be misidentified than white men.
4. “Companies can share my data without my knowledge”
Under data protection law, you have the legal right to be informed about how your personal data is being used. You can also legally halt or restrict the processing of your data and object to how it is being processed in certain circumstances.
According to the European Union’s General Data Protection Regulation (GDPR), sharing personal data can only be lawful if either consent is given or another legitimate basis exists. Examples of situations in which permission would be bypassed include when the data is needed to save a person’s life, when the information is required to comply with a legal obligation or when sharing that information is in the public interest.
“Except for a few very special cases, informed explicit user consent for any use of data is obligatory,” explains Andrew Bud, chief executive of iProov.
Biometric data has even stronger legal protection. It is one of nine special categories outlined in the Data Protection Act 2018, the UK’s implementation of GDPR, which means companies processing biometric data must have both a lawful basis and meet an additional condition to do so.
5. “Biometrics are expensive and aren’t cost effective in the long run”
Advances in technology mean the cost of biometrics is falling all the time. “Ultra-accurate face verification is now more or less free in the cloud from vendors such as Microsoft, Amazon and others,” says Bud at iProov. “This makes it possible for even small companies to develop very high-performance systems that cost very little to run.”
The benefit of bring-your-own-device strategies, which leverage widely adopted smartphones, mean biometric platforms require very little initial investment. “Plus, over time, the cost benefits will snowball; there are no additional fees to onboard new employees and no expensive hardware to regularly upgrade,” says Veridium’s Stickland.
As a result of what’s commonly known as “password fatigue”, many users are regularly resetting passwords and calling IT helpdesks. Veridium estimates that businesses with 10,000 employees spend around $1.9 million annually on password resets. So swapping or enhancing traditional password authentication with biometric data can also mean big cost-savings for businesses.
According to a report by the UK’s Department for International Development, when Nigeria launched its e-ID system it made an annual saving of $1 billion through exposing 62,000 so-called ghost workers in the public sector.
6. “Biometrics take longer to process than other forms of authentication”
Processing biometric data can be every bit as quick as other methods of verification and is faster in many cases.
“Typing in a password or getting a two-factor authentication code from an application, SMS or hardware key is substantially more time consuming than using a fingerprint or taking a selfie to authenticate,” says Goldsmith at Onfido.
As Anton Klippmark, product marketing manager at BehavioSec, points out: “The big premium is on gaining biometrics’ and behavioural analytics’ powerful anti-fraud data, without adding friction to the user experience, because if new security measures are too cumbersome to use, it breaks the mobile and convenience-based business models of apps and services.”