The accelerated shift to online over the past 18 months has been a boon to many businesses and a lifesaver for some. But with the rise in online activity has come an equivalent increase in cybercrime. With staff having to rapidly adopt remote working, the lines between business and personal technologies have become blurred, weakening organisations’ defences against the criminals. Attacks are varied and more sophisticated, ranging from malware and ransomware attacks to denial of service, domain spoofing and more.
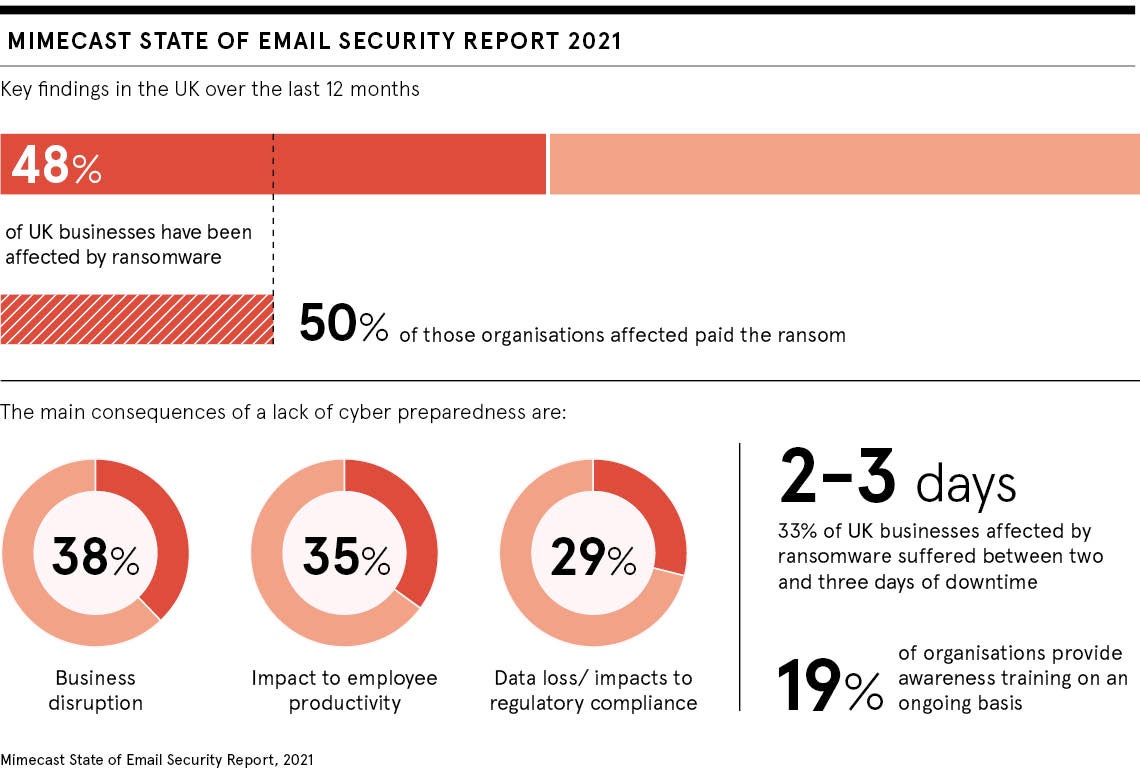
“The preeminent threat, for at least the last year, has been ransomware,” explains Mimecast’s head of risk & resilience, e-crime & cyber investigation, Carl Wearn, describing a common attack where companies’ systems are infiltrated and taken over by criminals who either shut down access or threaten to leak customer data unless paid a ransom – hence the name. The common perception of such criminals is a lone wolf, hacker or organisation with a political aim. The reality is much more ordinary. “The vast majority of ransomware attacks are opportunistic. It’s lucrative for the criminals and victims are reluctant to report it because of the impact on their brand reputation.”
But while the temptation might be to keep quiet and pay up, the threat to business and brand reputation doesn’t end there. “Not reporting it is a hindrance for law enforcement. In many cases, they are able to get some, or even all, of the money back from the criminals. But companies fear the resulting publicity will mean they are either open to a copycat attack, or that they might lose their customers’ trust from having fallen victim in the first place,” Wearn explains.
Despite the growing number of insurance products claiming to protect against cybercrime, payouts are by no means a given and, in some cases, the presence of coverage may actually encourage an attack. In most instances, companies should take simple steps to protect themselves against cyberthreats.
Cloud storage has become increasingly popular over the years and for good reason – it’s flexible, comparatively inexpensive and generally secure. But it’s important to be security conscious with any cloud storage or backups, as these can be targeted for encryption, like anything else.
Organisations should make sure they have fallback email and archive capabilities. “With a solution in place, even following an attack, you can continue to use email and carry on once you have restored from backup. Without that backup, once an attack has happened, it’s clearly too late,” Wearn warns.
Then it comes down to basic IT hygiene. Companies can take very basic steps to protect their systems. A strong password regime, for example, where regular changes are enforced, is the first line of defence. Awareness training is a key element here as employees must be aware of their role in cybersecurity. Multifactor authentication as standard is an additional layer of protection that is simple to institute. Segmenting networks so they can be cut off from the rest of the system and quarantined can prevent attacks escalating.
Company culture also plays an important part. “It’s not uncommon for senior staff to insist on having admin access to applications but this just introduces more weakness into the system,” Wearn suggests. “Resist the temptation to bow to job titles and restrict access to only the people who know how to keep those systems safe.” Businesses should be insisting on a separation between work devices and technology for personal use.
Increasingly, organisations are looking to leverage cyber intelligence across multiple systems. Mimecast uses specific APIs to help systems collaborate and share knowledge of threats across the security ecosystem. Ultimately, resisting malicious actors online comes down to a joint effort between business, employees, specialist vendors and consultants and law enforcement.
Wearn concludes: “Take the time to research and collaborate with cybersecurity experts and select ‘best of breed’ solutions to provide layered security that suits your needs best. Implement awareness training for all users. Security is everyone’s responsibility, particularly now we are all embracing a hybrid working model.”
For more information visit www.mimecast.com/times
Sponsored by

The accelerated shift to online over the past 18 months has been a boon to many businesses and a lifesaver for some. But with the rise in online activity has come an equivalent increase in cybercrime. With staff having to rapidly adopt remote working, the lines between business and personal technologies have become blurred, weakening organisations’ defences against the criminals. Attacks are varied and more sophisticated, ranging from malware and ransomware attacks to denial of service, domain spoofing and more.
“The preeminent threat, for at least the last year, has been ransomware,” explains Mimecast’s head of risk & resilience, e-crime & cyber investigation, Carl Wearn, describing a common attack where companies’ systems are infiltrated and taken over by criminals who either shut down access or threaten to leak customer data unless paid a ransom – hence the name. The common perception of such criminals is a lone wolf, hacker or organisation with a political aim. The reality is much more ordinary. “The vast majority of ransomware attacks are opportunistic. It’s lucrative for the criminals and victims are reluctant to report it because of the impact on their brand reputation.”
But while the temptation might be to keep quiet and pay up, the threat to business and brand reputation doesn’t end there. “Not reporting it is a hindrance for law enforcement. In many cases, they are able to get some, or even all, of the money back from the criminals. But companies fear the resulting publicity will mean they are either open to a copycat attack, or that they might lose their customers’ trust from having fallen victim in the first place,” Wearn explains.