The sudden mass shift to remote working amid the coronavirus crisis left many businesses not only scrambling to adapt their policies and processes, but also more exposed to cyber-threats. Spearphishing attacks grew by 667 per cent as countries entered lockdown in March, according to research by Barracuda, while the UK National Cyber Security Centre has reported COVID-related fraud reports quadrupled.
Ensuring employees could be connected to business systems from home meant IT teams had to act quickly to set up VPNs (virtual private networks) or other secure access options for users that had not worked remotely in the past. It also required swift investments in the necessary infrastructure, hardware and software, including the peripherals that help people work more effectively from home.
In many organisations, previously restricted practices have had to be discarded in favour of enabling productivity to continue with as little disruption as possible. Lawyers have taken case files home. Insurance claims have been processed remotely. Company mail has been redirected to personal addresses and documents downloaded to local drives to be printed on unsecured devices. That’s just paper documents; at the same time, spikes in cloud storage usage is driving a new way of dark data into businesses.
“The sheer pace and scale at which companies had to enable remote working has exposed them to risks,” says Marc Ueckermann, chief technology officer at Xenith, a leading provider of intelligent workplace services. “Cybercriminals and fraudsters have leveraged the opportunity to attack organisations while they are distracted and at their most stretched. Moving quickly does not allow for careful planning and mitigation of risks.”
Even when the pandemic is finally over, it is becoming increasingly clear that organisations won’t return to business as usual. Home working, it appears, is here to stay, certainly at far greater levels than before the virus emerged, and the ability of companies to support their remote workforce proactively will be a key differentiator in the years ahead. Doing this successfully will require the right technology enablement to ensure employees have the devices and access to data to work from home effectively.
“Critical approaches should always be aligned to employee engagement and productivity, with the end-client’s experience the essential metric of success,” says Ueckermann. “Ensure home setup is focused on employee wellbeing. Make sure these technologies can also play a role in creating an inclusive remote working culture. One of the greatest challenges is adding necessary layers of added security, but doing so in ways that aren’t intrusive and don’t affect the productivity of the end-users or the IT teams supporting them.”
Visibility across all employee devices, including their usage, when people are working from home will be particularly important in the “new normal” emerging from the pandemic. Organisations that can effectively monitor how devices are performing, and ensure a proactive resolution to potential issues so actions can be taken before failure, will maintain strong productivity and maximise employee satisfaction and engagement.
Meanwhile, with roles and responsibilities changing and new software, systems and processes continually evolving, it’s just as important that companies can ensure their employees have the right device to perform the tasks required of them. By monitoring existing device usage patterns, such as hard disk, processor and memory utilisation, and matching the functionality of devices with the tasks involved in certain jobs, it’s much easier for IT to select the appropriate equipment for each user.
“You can never get back time lost because equipment is not working as it should,” says Ueckermann. “That can be avoided when your IT team has the visibility to act proactively. Imagine the impact of IT reaching out to you and saying they’ve seen you’re experiencing some issues with your laptop so a replacement part or device is already on its way to you. In a time of redundancies, furloughing and pressure on employees to perform more tasks, nobody should have to deal with a malfunctioning device anymore.
“Visibility is also vital in terms of security monitoring and reporting. A significant point of entry for any attack is through end-user devices. Home working increases the risks of data breaches, which have serious data protection ramifications, but also significantly impact productivity because remote workers are disrupted. They can’t just walk down to IT, hand over the affected device and get a replacement unit. It might take days to get one. By monitoring devices, proactive actions can be taken to protect the business.”
The key to businesses gaining this visibility during the COVID-19 crisis has been device-as-a-service (DaaS), a solution by HP. Health and usage analytics from HP Proactive Management, which sits at the heart of the solution, monitors and reports device performance and status, including installed software, operating system version, application usage, hard drive usage, CPU (central processing unit) utilisation and device health.
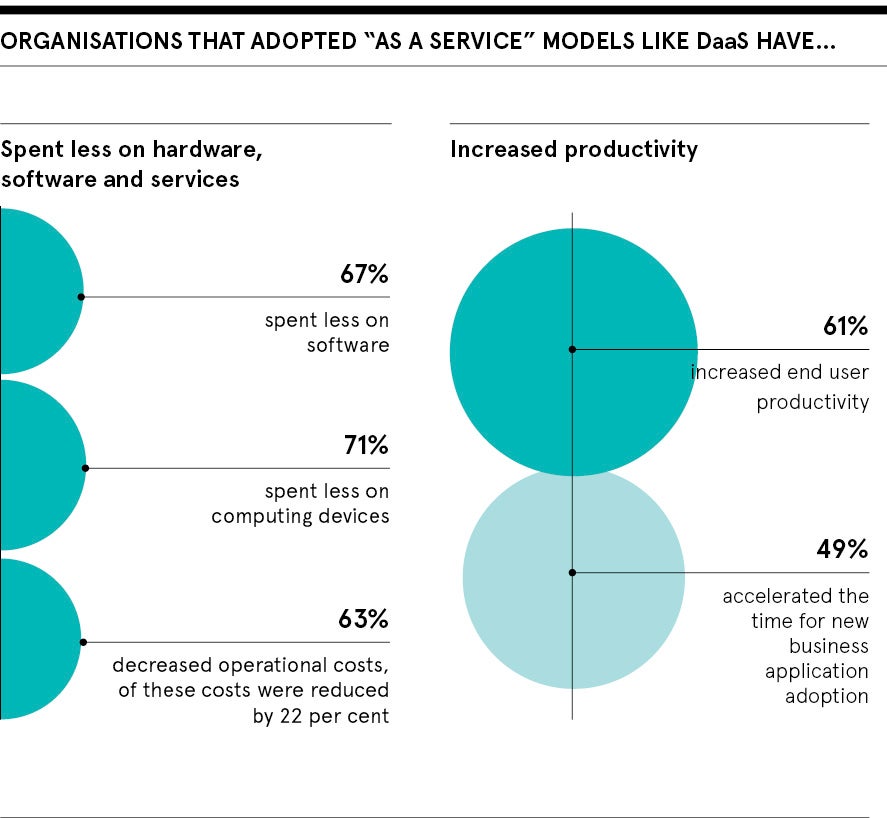
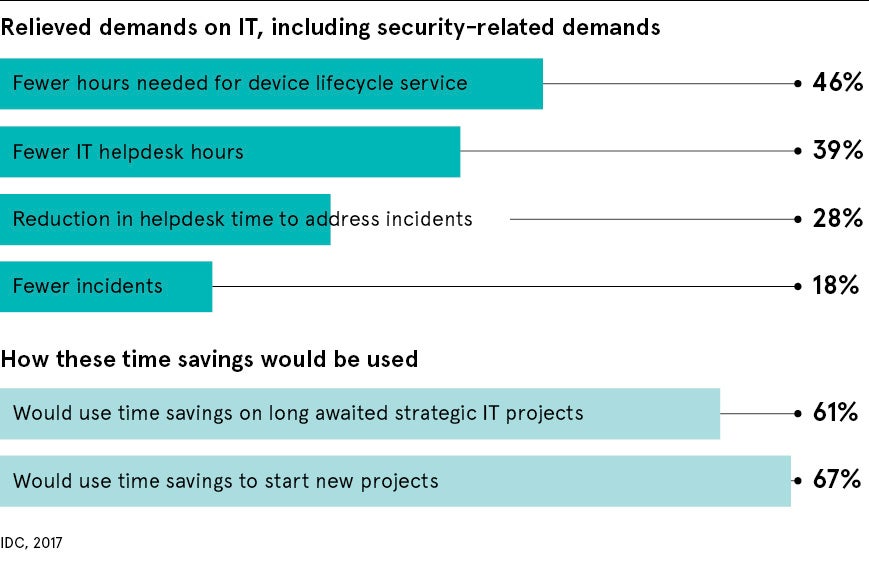
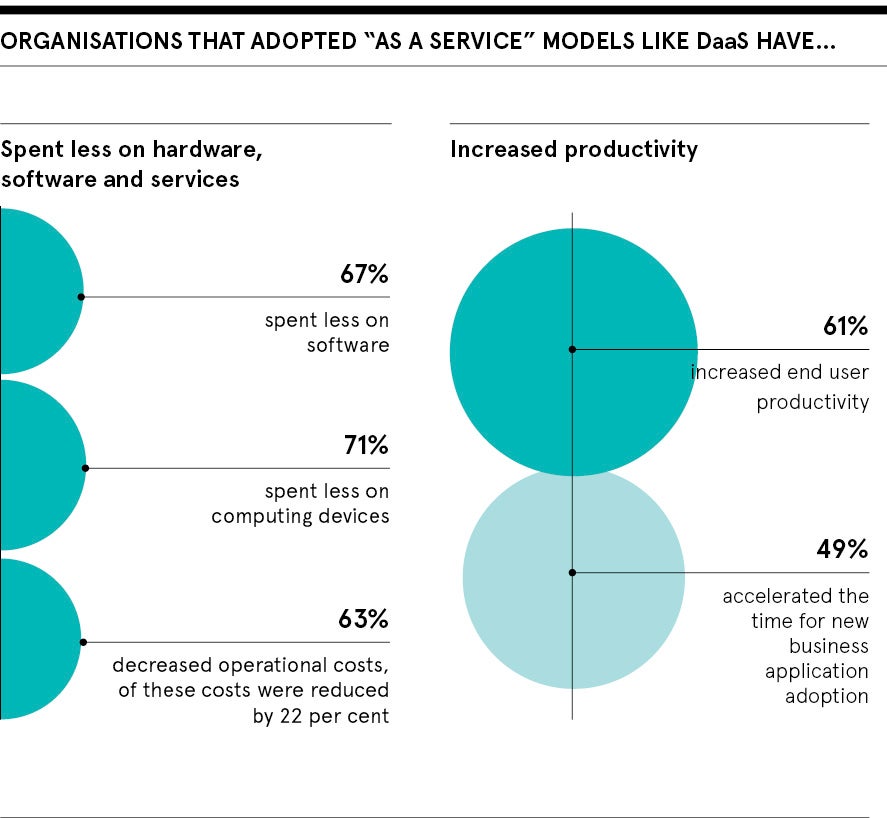
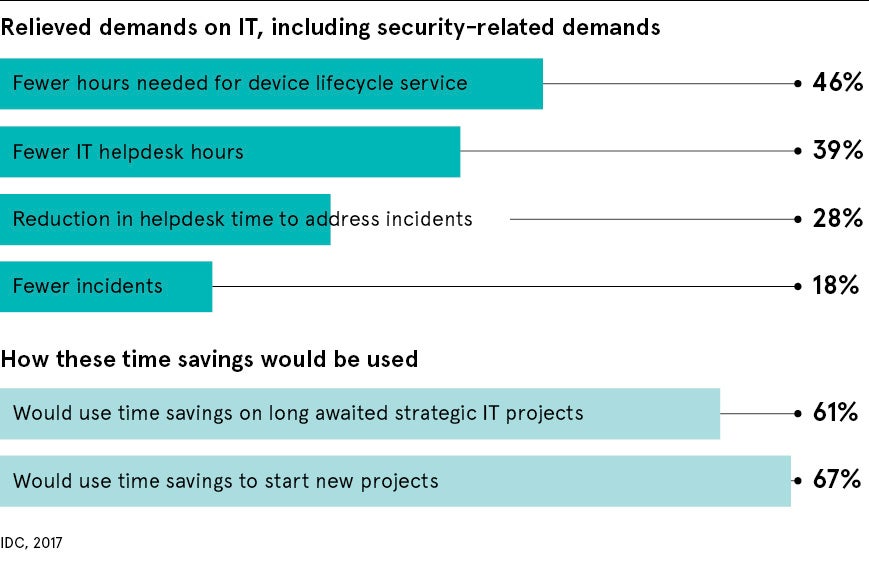
Going beyond the hardware, DaaS is a life cycle management programme for end-user devices, allowing businesses to adopt a flexible consumption-based model for hardware provision while reducing the management overhead and providing high levels of security. This not only makes HP DaaS an attractive proposition from a financial perspective during difficult economic conditions, but it also frees up vital time for in-house IT support teams so they can focus on other business-critical tasks.
Security isn’t just enhanced by the visibility enabled by the solution and the ability to be more proactive; there are also many security features built in to contain and eliminate threats. The solution goes well beyond standard security practices by harnessing the power of deep-learning artificial intelligence to provide real-time threat detection, self-healing BIOS (basic input/output system) and hardware-enforced secure browsing that isolates web content in a virtual machine.
As an HP Gold Partner, Xenith has dedicated DaaS experts and has played an important role in deploying the solution for clients adapting to the new normal, while offering access to an extensive support team globally.
“Now is the time to make sure the quick actions taken to get everyone working from home are now formulated into proper strategies with investments in ensuring remote work practices are the norm, not the exception,” says Ueckermann. “It is essential to monitor your environment, visualise areas of concern and adjust work practises, processes and strategies to align to the ever-changing customer and employee needs, and indeed any further disruption if a second wave should emerge.
“HP DaaS offers a plethora of hardware options for every requirement, including processors from AMD, the world’s only processor family with full memory encryption as standard, to help defend against cold boot attacks. AMD’s latest processors offer incredible speed, mobility and battery life, with up to eight cores in ultraportable devices, and battery life which extends to up to 24 hours and 15 minutes on some models.”
To learn more, book in a 15min chat with Xenith’s specialist.
As a special offer for Raconteur readers, you are eligible for free access to the HP Management & Security Tool for 60 days, giving you actionable insight on more than 30 variables regarding your existing hardware fleet (any brand) security and usage patterns.
Tel: 020 7417 2000
Email: [email protected]