Enterprises have for too long taken a siloed approach to digital identity processes. Different data structures are owned by different departments, who often have contrasting, even competing, objectives when it comes to onboarding and managing users. The compliance group examines personal data in light of various regulations while the risk group looks to reduce fraud losses, and it’s all independent of the product management and customer support departments.
Such fragmentation is creating friction-filled experiences and consumer frustration, while national and international silos at a data level are also inhibiting companies from learning from identity insights outside of their own organisation. Privacy concerns have understandably fuelled data protectionism, however new tech advancements now mean encrypted data signals can be shared to bolster fraud defences without any identifiable user information being shared.
The business challenge of a fragmented digital identity
Fraudsters know how debilitating silos can be, which is why they not only seek to exploit them in the businesses they attack but also avoid them in their own activities by embracing networks. To combat synthetic fraud, which already accounts for 15 per cent of credit card losses, according to Experian, and is the fastest growing type of financial crime, organisations must partly learn from the fraudsters themselves.
“The way cybercriminals behave is not siloed at all, it’s networked, so how do we fight them in the same way? We’re learning that businesses have to be adaptive and collaborative in order to compete,” says Carey O’Connor Kolaja, CEO at identity management and intelligence company AU10TIX, whose solutions link physical and digital identities so companies and consumers can confidently connect.
“Identity has traditionally been thought about in terms of what needs to be known to verify access to something particular. If I want to buy alcohol, I have to show my ID but the seller only needs to verify I’m over the legal drinking age. If I want to get a loan from a bank, there’s a lot more about me and my financial suitability that must be shared.
“Over time, identity is not just a government issued ID or a digital footprint – it’s an accumulation of information that describes you and your behaviours, meaning identity becomes much bigger than we ever realised, as do the opportunities for cybercriminals. We’re seeing fraud attacks from the most unexpected places with PII not necessarily acquired from a full account takeover but through skimming small bits of information from unsuspecting sources.”
The unified fight against synthetic fraud
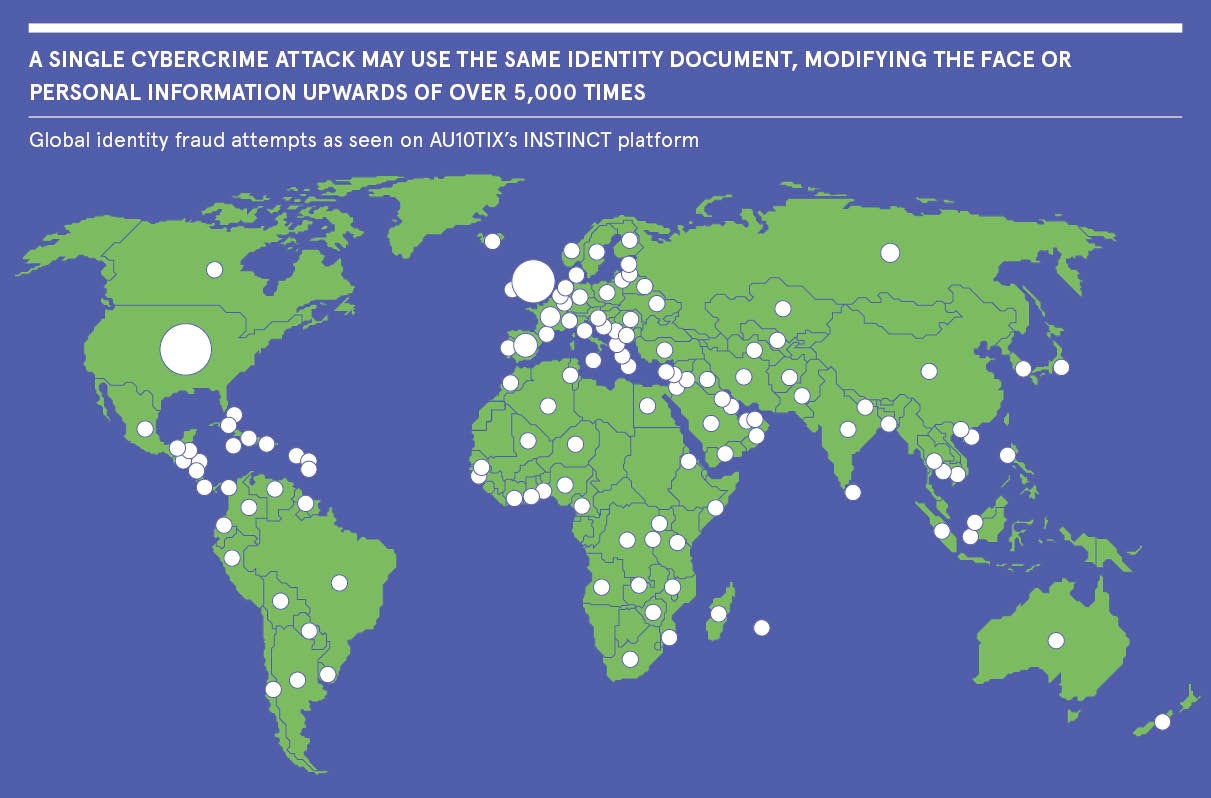
AU10TIX’s has transformed from developing technology identity verification for border control and airport security to identity intelligence that supports customer due diligence and onboarding for brands like Google, PayPal and Uber. Its unique heritage gives it a strong edge in understanding what happens across the physical and digital divide, and has allowed it to launch INSTINCT, a synthetic fraud detection solution that is able to verify the authenticity of an identity through data signals alone. This will enable a global network of data signals that aids companies in fighting fraud together.
“When you start to look at synthetic fraud over a continuum, you can really unearth where the perpetrators are,” says O’Connor Kolaja. “We’re catching 50 synthetic identity attacks in any one company on a given day. Most importantly, we’re able to not only stop synthetic fraud in one network or ‘closed garden’, but safely share the intelligence with other organisations around the world so they can prevent the same attack from happening again – continuously updating a synthetic identity watch list.
“Covid-19 has created an environment where people are concerned more about cyberattacks than terrorist attacks. It has forced identity protection to the forefront of our minds and amplified the need to understand how, through technology, our identities and behaviour can be used to equalise and authenticate our access to all life’s experiences. We have to grasp this opportunity to accelerate unification and adaptive identity processes, advancing our progress to a more secure and inclusive world.”
For more information, visit www.au10tix.com
Sponsored by

Enterprises have for too long taken a siloed approach to digital identity processes. Different data structures are owned by different departments, who often have contrasting, even competing, objectives when it comes to onboarding and managing users. The compliance group examines personal data in light of various regulations while the risk group looks to reduce fraud losses, and it’s all independent of the product management and customer support departments.
Such fragmentation is creating friction-filled experiences and consumer frustration, while national and international silos at a data level are also inhibiting companies from learning from identity insights outside of their own organisation. Privacy concerns have understandably fuelled data protectionism, however new tech advancements now mean encrypted data signals can be shared to bolster fraud defences without any identifiable user information being shared.