When it comes to your vulnerability to cyber attack, if your main source of comfort is that at least the perpetrators have to marshal an army of talented hackers creating bespoke code to infiltrate your organisation - you’d better think twice.
“You can pick ransomware up off the shelf as a service, should you be so inclined. It’s relatively quick and easy to get your hands on and to execute, and once it gets in somewhere, it’s very destructive and disruptive,” warns Johan Dreyer, Mimecast EMEA field chief technology officer.
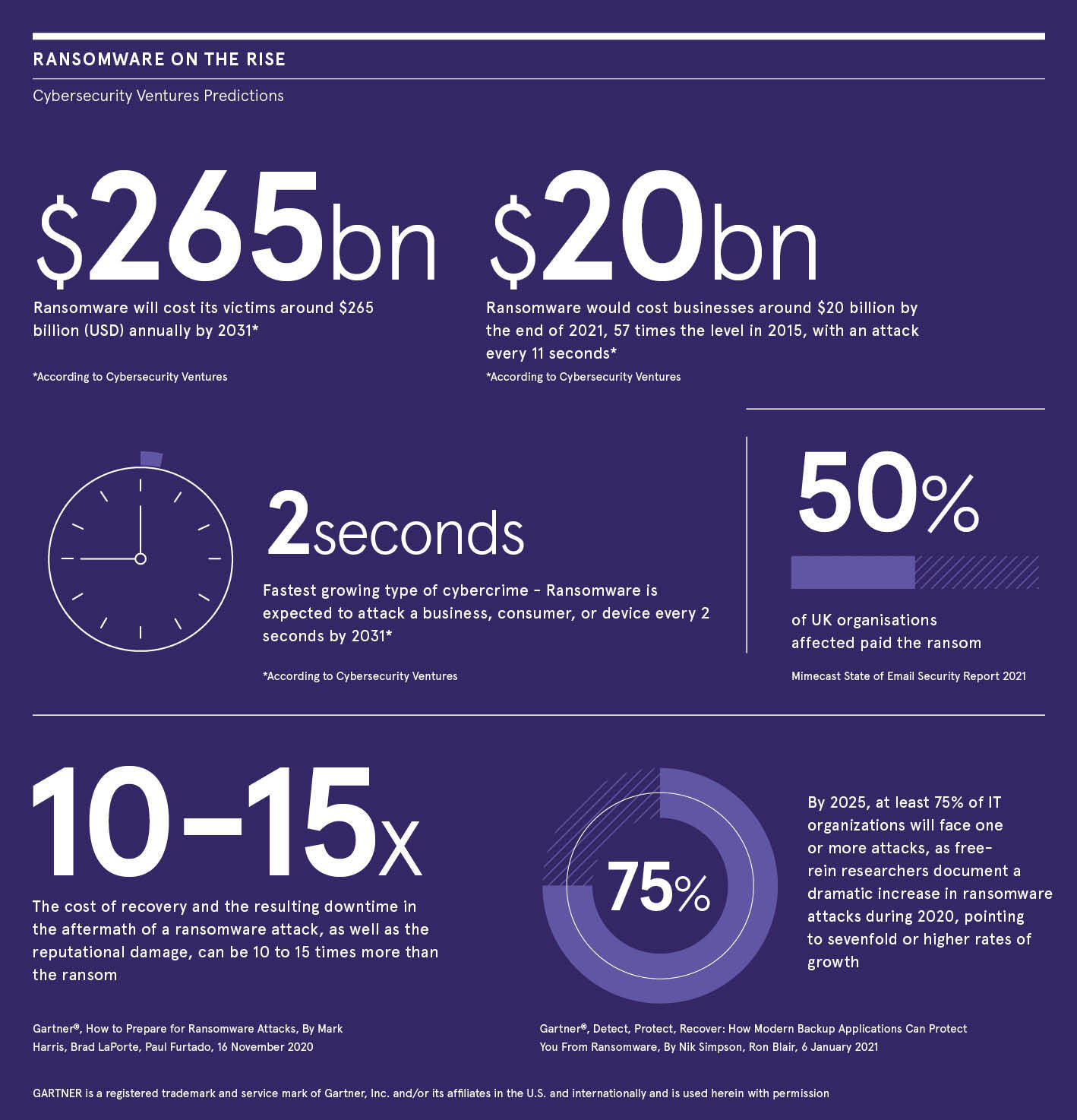
As a result, it’s clearly becoming the cybercriminal’s weapon of choice. According to Mimecast’s State of Email Security Report, 2021, 48% of UK businesses have been affected by ransomware, 33% of those affected suffered between two and three days of downtime and 50% have paid the ransom in the past year. Those that suffered an attack were down for an average of six days and a third of those who paid the ransom to release their data ultimately didn’t get it back.
Before the pandemic struck, Cybersecurity Ventures noted that ransomware was predicted to cost businesses around $20bn by the end of 2021, 57 times the level in 2015, with an attack every 11 seconds. In a work-from-home environment, businesses were more at risk than ever. There was a 60% increase in the use of company computers for personal reasons, 34% of Brits and Germans were found to be opening suspicious emails and there was a three-fold increase in unsafe clicks by employees.
Why is ransomware so destructive? Aside from the ease with which bad actors can get hold of it and deploy it in a short time period, it preys on companies’ common failings when it comes to cyber preparedness. Cyber criminals rely on the fact that businesses have no way to access the data that has been locked up by the ransomware, other than to pay them to release it.
The reason criminals are holding companies to ransom so successfully is because too many still don’t have a comprehensive backup regimen. In the best-case scenario, a business subject to a ransomware attack would review how the bad actors were able to get in, resolve the weakness, restore from backup and proceed as normal with minimal impact.
However, for most this is very much a case of shutting the stable door after the horse has bolted. In many cases, companies have a perfect storm of poorly updated systems, meaning patches designed to remove vulnerabilities have not been installed, backups are delayed or irregular and the organisation hasn’t got the resources or resilience to continue with business as usual while they try to recover their data. The only solution is to pay up and hope for the best.
“The unfortunate reality is that there may be no way to unlock what they’ve done. Many organisations have paid ransoms and not received their data. Even when they do, you are still fuelling a criminal economy. It all goes back to making sure your systems are adequately backed up with a sensible redundancy in place. We offer organisations a copy of their email archive which maintains their ability to send and receive email after an attack,” Dreyer insists.
Becoming ransomware-resilient starts at the very top. “It can be a cliché that the board is responsible but to a degree, it is. Taking action is typically down to the chief information officer or the head of security. To help them play their part, the board has to set out the strategy that the executive can carry out, implementing drills to prepare the business, model best practice based on past events and improve the organisation’s overall cyber resilience skillset which ultimately empowers security as a culture,” says Dreyer.
How the CIO’s role is perceived is critical to building a cybersecure environment and it’s a role that has undergone significant change. Before, it may have been seen as a purely technical role, now the position is populated by people whose remit is business first and technology second.
Part of the shift is around understanding how technology and the CIO contributes to business value. They are increasingly seen as partners in the creation of business value in the first instance, and there to protect it in the second. Security professionals have to be able to tie the risks that they’re facing more closely to business value and business objectives. Why? Because ransomware puts value at risk as it can prevent businesses from serving their customers and therefore has a material impact.
We’re actively collecting intelligence and sharing it with systems such as end point detection and response or SOAR and that enriches their data set
“It’s more about driving business outcomes rather than providing technology for the sake of it. There’s a sense of accountability,” Dreyer says.
“Most organisations have some protection in place,” Dreyer adds. “Mimecast’s strengths are in email security, continuity, and archive and our systems are thwarting attacks day in, day out.” Mimecast protects against phishing and BEC (business email compromise) attacks designed to capture credentials that can be used to deploy ransomware. “We continue to invest heavily in digital asset monitoring and asset protection. Active monitoring is an essential weapon in the fight against cybercrime and one that is very much a collaborative effort.
“When it comes to protecting your business there’s no magic tool or silver bullet so Mimecast’s investing in integrating with other security vendors. We’re actively collecting intelligence and sharing it with systems such as end point detection and response or SOAR (Security Orchestration and Remediation) and that enriches their data set. Customers can also ingest intelligence from other sources into their Mimecast Service to complete the circle. We are very much advocates of a ‘better together’ strategy,” Dreyer reveals.
With many organisations making the move to remote and, latterly, hybrid working, companies need to be more vigilant than ever that their cyber protocols are as robust as possible. Ransomware attacks are almost an inevitability in today’s world. Cyber hygiene is an essential part of every organisation’s strategy. Actions like reviewing your patch regime, keeping systems up-to-date and keeping an eye on backups are vital.
Finally, prevention is always better than cure. Attacks are most likely when employees simply click on unsecure emails or are browsing unauthorised sites while on business networks so education is paramount. Building a culture of security awareness that applies to both employees’ personal and business environments.
“Even the most sophisticated organisations can and have been breached but, we are seeing more openness and transparency which gives everyone else the information they need to better protect themselves. The more we can share intelligence, the more we can uplift the community. That’s why we open our systems and platforms so our customers and partners can all benefit.”
Learn how to mitigate the ransomware risk with our free resources:
mimecast.com/timescio
Promoted by Mimecast

When it comes to your vulnerability to cyber attack, if your main source of comfort is that at least the perpetrators have to marshal an army of talented hackers creating bespoke code to infiltrate your organisation - you’d better think twice.
“You can pick ransomware up off the shelf as a service, should you be so inclined. It’s relatively quick and easy to get your hands on and to execute, and once it gets in somewhere, it’s very destructive and disruptive,” warns Johan Dreyer, Mimecast EMEA field chief technology officer.
As a result, it’s clearly becoming the cybercriminal’s weapon of choice. According to Mimecast’s State of Email Security Report, 2021, 48% of UK businesses have been affected by ransomware, 33% of those affected suffered between two and three days of downtime and 50% have paid the ransom in the past year. Those that suffered an attack were down for an average of six days and a third of those who paid the ransom to release their data ultimately didn’t get it back.