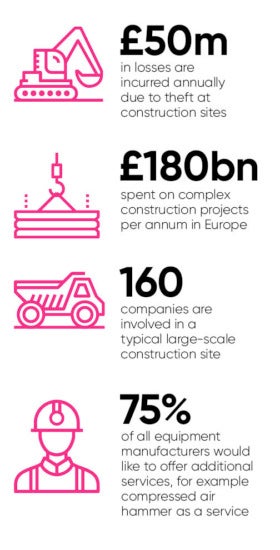
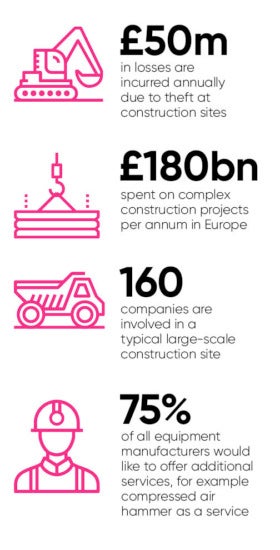
 Construction companies track millions of dollars’ worth of equipment and materials as they are moved around building sites, while farmers maximise crop yields by fitting harvesting machinery with sensors, transmitting data back to base for analysis.
Construction companies track millions of dollars’ worth of equipment and materials as they are moved around building sites, while farmers maximise crop yields by fitting harvesting machinery with sensors, transmitting data back to base for analysis.
A new industry touted as servitisation is being created, where rather than sell products, manufacturers are renting out hardware such as aircraft engines and diggers. Internet of things (IoT) sensors measure usage for billing and can monitor wear so engineers can fix machines before they break.
However, amid the euphoria and race to interconnect, there is a problem yet to be addressed. We’ve heard too many stories of security breaches as a result of hastened IoT implementation. Some are trivial, resulting in minor issues that become cautionary tales, while others are terrifying in their potential for damage.
In 2015 a WIRED magazine reporter participated in an experiment involving the hacking of a Jeep Cherokee while it was travelling at 70mph. This involved the experienced hackers traversing the internet to take control of steering, brakes, air conditioning and wipers, all while sitting comfortably in a house ten miles away.
We need a wake-up call. Without a robust and reliable security model in place, opening the door to IoT capabilities is like pouring water on cracked concrete – it will expose your environment, permitting undesirable content to find a way in through every hairline fracture in your infrastructure.
The truth is implementing an IoT strategy needs a rethink in the way we address both security and privacy. For anyone formulating an IoT plan, there are key steps to take.
Secure network
The first action is to engage your security division, through the chief information security officer (CISO). The CISO needs to be involved from the outset in all board-level discussions around the notion of entering the IoT space. It is the CISO who understands the current business models, the security guarding this space and the technologies involved in IoT adoption. The CISO is the nexus between technological security and business acumen.
Once engaged, the security team can ensure the existing processes are ready for the new flow of data that will be provided by IoT device incorporation. They know who else to engage. Your new working group must understand the scope and risk, and perform a calculated investigation. Does your existing network architecture have capacity to handle this influx of data? Is there sufficient space on your storage area network or cloud to hold the volume of data that will be received through these devices? Do you have the relevant accreditation and compliance to handle the sort of data you are preparing to gather and store?
The working group will explore many topics including security, network, storage, server, process, governance, privacy and more. The clearer the picture, the easier it is to work with the business to ensure a successful integration of IoT capability.
By getting these foundational steps right, the CISO should orchestrate the required activities with the confidence of the business and the support of a service integrator with expertise in security and communications.
Regulation
Look at regulation, but do not rely on it. Complacency in the IoT industry has many sources. A major one is the trust consumers and companies have in regulation, although on the surface this does seem reasonable. Ofwat guarantees clean water and the Legal Ombudsman keeps lawyers on the straight and narrow. But the internet of things has not yet reached maturation and neither security nor privacy are satisfactorily covered by legislation.
IoT devices by their very nature can be constructed from inexpensive components and connected to the internet with ease. Many do not function in a way that is understood by classical infrastructure and the industry is full of creative, but unreliable actors.
While mainstream vendors can be monitored for conformance with regulation, the relative low cost of entry allows virtually anyone access to IoT technology. This enables individuals to expend maximum effort to advance capabilities, with no pressure to adhere to any regulations in place. This means private information can be transmitted from unlicensed IoT devices, not adhering to the standard telecommunication regulations enforced on large vendors.
Recently the IoT Alliance Australia published their Internet of Things Security Guidelines, by which they aim to help industry understand the measures that must be taken to ensure practical application of security within the field of IoT. This is one of the first open publications of its kind, aimed at both educating corporations and proposing measures to tackle the concern around the security of the IoT. I highly recommend reading it.
Your security team needs to understand the state of legislation, but also what it doesn’t cover. The New General Data Protection Regulation requirements mean there’s a renewed focus on the law. Now is an ideal to time to get up to speed.
Partner up
The tantalising potential of IoT means the only option is to engage. But the security and data concerns will be hard to master alone. A proven method is to join forces with a specialist in the field.
As a global force in the communication world, T-Systems is renowned for its cutting-edge work across innovative fields. In IoT, this includes solutions spanning manufacturing, the digital world, and the consumer space. Our approach is that security must be engrained in the heart of IoT and we offer services covering the three fundamental security pillars: prevent, detect and respond.
Within this space, T-Systems has a number of offerings that help analyse, report on and then prepare corporate environments in readiness for entry into the IoT. These services range from cyber defence and cloud security, to leading-edge technology such as drone defence solutions. We are constantly looking at the next threat vectors and working on ways to mitigate these attacks through robust services and solutions.
It’s time to unleash IoT. We are on the cusp of incredible new services and concepts. Yes, there are challenges, but with the right approach they can be overcome. Together we can make the most of this incredible opportunity. The only limit to the potential of the IoT is our creativity.
To find out more please visit t-systems.co.uk/iot
Secure network